The Kaspersky Global Research & Analysis Team has uncovered a malware-as-a-service campaign targeting ebook readers across Turkey, Egypt, Bangladesh and Germany. Cybercriminals are disguising sophisticated malware as bestselling Turkish and Arabic books, tricking hundreds of readers into downloading files that steal passwords, cryptocurrency wallets and other sensitive information from their computers.
Kaspersky has identified a malware-as-a-service (MaaS) campaign that is using LazyGo, a newly discovered Go-based loader that delivers multiple information-stealing programs. The campaign targets users searching for popular titles ranging from John Buchan’s “The Thirty-Nine Steps” in Turkish to Arabic texts on poetry, folklore and religious practices. The fake ebooks span diverse interests, including also Turkish business management texts like Tamer Koçel’s “İşletme Yöneticiliği,” contemporary fiction, and Arabic literary criticism such as “The Literary and Linguistic Movement in the Sultanate of Oman.”
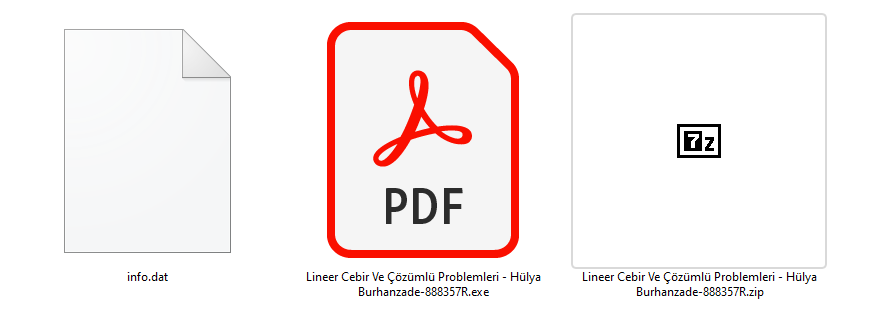
The malicious files masquerade as PDF ebooks but are actually executable programs with PDF icons. When users download and open these fake books, the LazyGo loader deploys infostealers including StealC, Vidar and ArechClient2. Kaspersky researchers identified three variants of LazyGo, each employing different evasion techniques such as API unhooking, AMSI bypass, ETW disabling and anti-virtual machine detection.
The information that the attackers steal includes:
- Browser data: Saved passwords, cookies, autofill information and browsing history from Chrome, Edge, Firefox and other browsers.
- Financial assets: Cryptocurrency wallet extensions, configuration files and storage data.
- Developer credentials: AWS credentials, Azure CLI tokens and Microsoft Identity Platform tokens.
- Communication platforms: Discord tokens, Telegram Desktop data and Steam session files.
- System information: Hardware specifications, installed software and running processes.
Victims infected with ArechClient2/SectopRAT face additional risk as attackers gain complete remote control over compromised machines.
“What makes this campaign particularly concerning is its use of a malware-as-a-service model combined with highly targeted social engineering,” said Yossef Abdelmonem, Senior Security Researcher at Kaspersky GReAT. “The LazyGo loader’s multiple variants and sophisticated evasion techniques show this isn’t opportunistic cybercrime – it’s a structured operation designed to harvest credentials at scale. Organisations should be especially vigilant as stolen developer tokens and cloud credentials can provide attackers with deep access to corporate infrastructure.”
Kaspersky telemetry shows that the campaign is affecting government agencies, educational institutions, IT services and other sectors. The campaign remains active with threat actors continuously uploading new malicious ebooks to GitHub and compromised websites.
Kaspersky experts recommend users verify ebook sources before downloading, carefully examine file properties, and maintain updated security software capable of detecting evasive malware techniques. When selecting a security solution, it’s advisable to choose one with robust anti-malware capabilities that have been validated through independent testing. According to a recent evaluation by AV-Comparatives, Kaspersky Premium demonstrated strong performance with a malware protection rate of 99.99% on a test collection of 9,995 files, proving high-level defense against malicious software.