Monday, 28 July 2025; Kaspersky researchers have discovered a new wave of scam attacks that use Google Forms to target crypto users. Knowing the email address of the potential victim, the attackers send a scam email through Google Forms, which is designed to appear as a notification from a crypto exchange service. Users are invited to receive an alleged transfer in cryptocurrency by following a link to a website where they are instructed to contact “blockchain support” and make a “commission” payment in crypto to receive the transfer. Following these instructions could lead to the loss of funds, as the whole “transfer” story is a hoax.
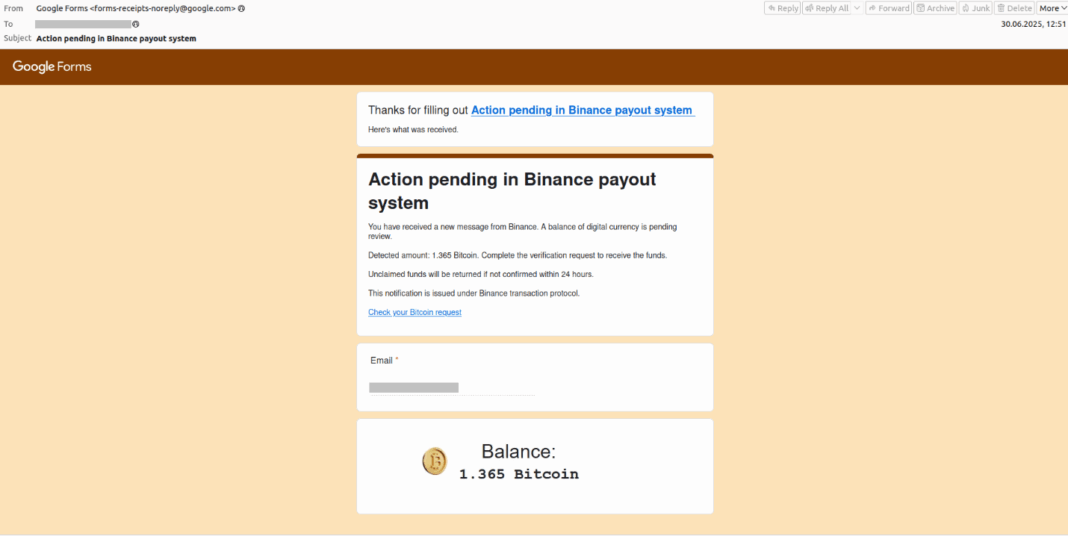
The attackers used Google Forms – a free tool for online surveys – to create a short questionnaire with just one slot to fill in: the email address. The attackers themselves input the victim’s email address into the form, and then Google Forms sends a questionnaire submission confirmation email to the victim. The attackers crafted this form submission confirmation to look like a notification from a crypto transaction service – indicating a sum to allegedly be paid out, urging the user to click on the link to receive the payout before it “expires”.
The scam email contains Google Forms attributes, such as a header with Google Forms logo, a link to the questionnaire (which the user never filled in), and the field value that had been submitted. The attackers bank on the fact that the email passes through spam filters, since it was sent from a legitimate Google address and the user is tricked by a catchy headline.
“This campaign demonstrates a cunning exploitation of a trusted and widely used platform to deliver scam attacks on cryptocurrency users. By crafting fraudulent submission confirmation emails that mimic legitimate notifications from crypto exchanges, attackers used the platform’s credibility to bypass email filters, and also the victim’s unfamiliarity with its format to lure them into divulging sensitive wallet credentials. There is a critical need for users to verify email sources, scrutinise links and adopt robust security measures to protect their digital assets,” comments Andrey Kovtun, Email Threats Protection Group Manager at Kaspersky.
After clicking on the link in the email, the user is directed to a scam website mimicking a crypto transaction platform.
To avoid falling victim to such attacks, Kaspersky recommends:
- Do not tap or click links in messages you weren’t expecting.
- Check for any unusual attributes in the email, like those pertaining to Google Forms that were described above.
- Install a reliable security solution such as Kaspersky Premium that would prevent the user from opening a scam website.